Quality to WOW your audience — delivered on time and on budget.
We consider printing a craft, expect each job to have unique requirements, and we are a G7 Master Qualified Facility. G7 is a revolutionary process developed by IDEAlliance and is based on principles of digital imaging, spectrophotometry, and computer-to-plate technologies. To you, it simply means that your finished print materials will look beautiful, consistently and repeatable across different devices and substrates.
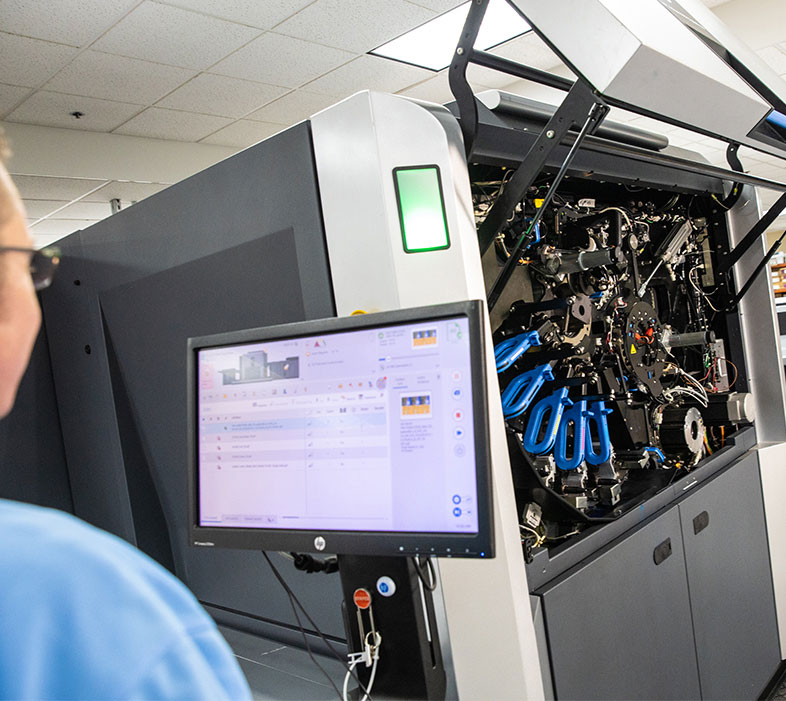
We have industry-leading technology to get the job done — fast.
We reinvest each year to ensure we are always offering the most cutting-edge printing capabilities and equipment. To protect your deadlines, we also have built-in equipment redundancies in every department.
If you have any questions regarding our equipment, please don't hesitate to contact a member of our sales team.
View Equipment